Configure OpenVPN Command Line Interface (CLI) on Raspberry Pi (Debian) using this comprehensive guide. Set up secure and private VPN connections through the command line interface, enhancing your online security on your Raspberry Pi.
- A working installation of Debian 11 (Debian Bullseye)
- A PureVPN premium account (Don’t have one? Sign up now!)
- Firstly, you will need to install OpenVPN packages and files. Type the following to install them:
- sudo bash
- sudo apt-get install openvpn
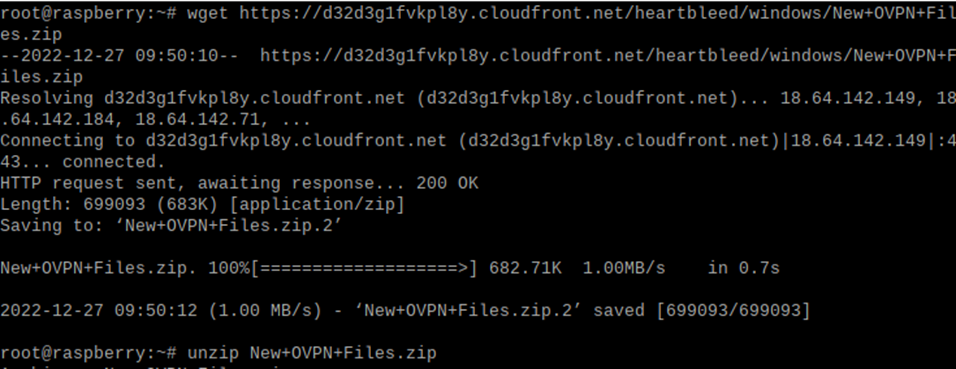
- Run the command to download PureVPN OpenVPN files and unzip/extract them.
wget https://d11a57lttb2ffq.cloudfront.net/heartbleed/router/Recommended-CA2.zip
unzip New+OVPN+Files.zip
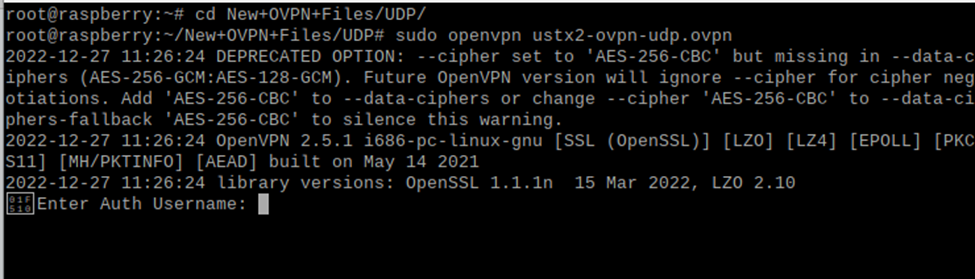
- Now access the directory where the openvpn files are downloaded and select either TCP or UDP location.
- cd New+OVPN+Files/UDP/
- OR
- cd New+OVPN+Files/TCP/
- Now to connect to the VPN, run the command:
sudo openvpn ustx2-ovpn-udp.ovpn
- (In this case the USA UDP server is used to connect to the VPN as an example. You are free to choose any server that best fits your requirements. In order to view all available servers and their names, press the Tab key twice immediately after sudo openvpn)
- You will be immediately prompted to enter the Auth Username and Auth Password, enter your PureVPN username and its password respectively.
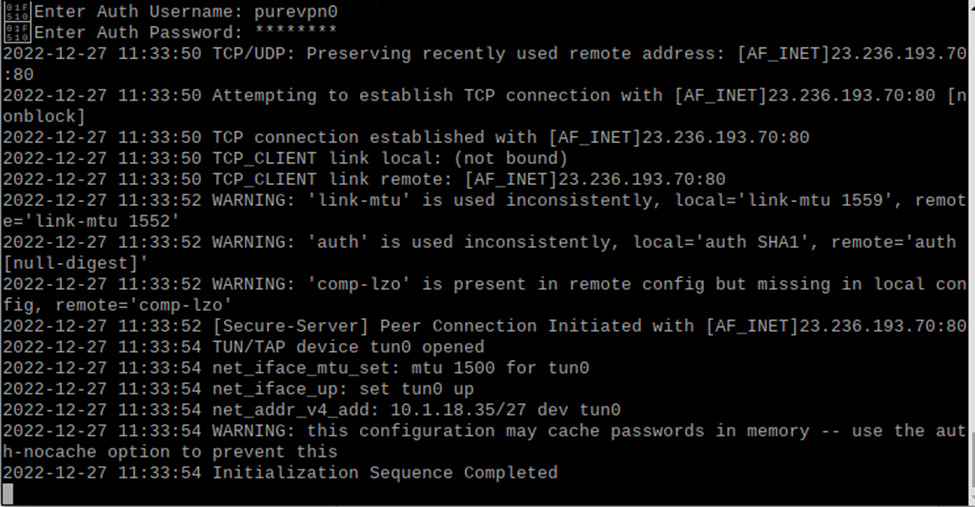
- You are now connected to PureVPN.
- In order to disconnect the connection, run this command:
sudo killall openvpn